Alleged Creator of Bitcoin Fog Arrested in Los Angeles
~4 min read | Published on 2021-04-29, tagged DarkWeb, Money-Laundering using 879 words.
The alleged owner of Bitcoin Fog, the “longest-running bitcoin money-laundering service on the darknet,” was arrested in Los Angeles.
According to the United States Department of Justice, Roman Sterlingov, 32, has operated Bitcoin Fog since 2011. During its operation, Bitcoin Fog moved 1.2 million Bitcoin worth $335 million at the time of the transactions.
The bulk of this cryptocurrency came from darknet marketplaces and was tied to illegal narcotics, computer fraud and abuse activities, and identity theft.

IRS-CI cyber analysts identified direct deposits into Bitcoin Fog from at least 35 darkweb markets. Below are the top five markets by U.S. dollar value of deposits:
Agora Market, 41,966.87 Bitcoin ($14,398,754.73) Silk Road 2.0 Market, 22,863.74 Bitcoin ($12,518,636.97) Silk Road Marketplace, 377,102.74 Bitocin ($9,556,159.49) Evolution Market, 11,100.79 Bitcoin ($3,199,542.15) AlphaBay Market 5,442.86 Bitcoin ($2,907,508.67)
IRS-CI cyber analysts identified funds sent directly from Bitcoin Fog to at least 51 different darknet markets. Below are the top five markets by the dollar value of sends:
Agora Market 26,398.12 Bitcoin ($8,680,430.34) Silk Road 2.0 Market 11,274.21 Bitcoin ($5,871,831.33) Silk Road Marketplace 106,522.77 Bitcoin ($2,289,509.42) Evolution Market 6,473.24 Bitcoin ($1,860,053.75) AlphaBay Market 3,375.90 Bitcoin ($1,557,931.95) Attribution
An analysis of bitcoin transactions, financial records, internet service provider records, e-mail records, and additional investigative information, identifies Roman Sterlingov as the operator of Bitcoin Fog, according to a Criminal Complaint filed in the District Of Columbia District Court.
Early in the investigation, investigators with the Internal Revenue Service-Criminal Investigation (IRS-CI) associated Bitcoin Fog with the Hotmail address [email protected]. An account on the BitcoinTalk.org forum had announced the launch of Bitcoin Fog (Here is the archived announcement on BitcoinTalk.org). The person responsible for creating that account had signed up with the above Hotmail address and the name “Akemashite Omedetou.” Records from Microsoft pertaining to [email protected] revealed that the account was created on October 7, 2011, using an apparent fake name via a virtual private network. The account on BitcoinTalk.org included details about the Bitcoin Fog service, including the service’s clearnet URL, bitcoinfog.com.
Bitcoinfog.com was registered through Highhosting.net on October 25, 2011. WhoIs records showed that the domain was registered to “Akemashite Omedetou” with the email address [email protected]. Records from Highhosting.net revealed that Akemashite Omedetou used a Liberty Reserve account to pay for the domain. Liberty Reserve records showed that the account was registered to [email protected]. Investigators reviewed account activity associated with the Liberty Reserve account and linked Sterlingov to “a series of layered transactions through multiple payment platforms.”
Specifically:
On September 29, 2011, according to records from the virtual currency exchange Mt. Gox, Sterlingov opened an account in his true name at Mt. Gox (Mt. Gox Account 1), using the email address [email protected]. On October 3, 2011, Sterlingov funded Mt. Gox Account 1 with 100 euros. On October 19, 2011, Mt. Gox Account 1 sent 36 BTC through an off-platform Bitcoin address to a second Mt. Gox Account (Mt. Gox Account 2) (registered to “[email protected]”). On October 20, 2011, Mt. Gox Account 2 sent 35 BTC to a third Mt. Gox Account (Mt. Gox Account 3) (registered to “[email protected]”). On October 20, 2011, Mt. Gox Account 3 sent $80 to an account at Aurum Xchange (Aurum Xchange Account 1), another digital payment platform. On October 20, 2011, Aurum Xchange Account 1 sent $76 to Liberty Reserve Account 1. On October 25, 2011, Liberty Reserve Account 1 paid the domain fees for www.bitcoinfog.com to Highhosting.net.
Investigators analyzed the IP addresses used to access the above Liberty Reserve and Mt. Gox accounts. The analysis revealed Sterlingov as the common owner, according to an IRS-CI Special Agent Devon Beckett. For example, on November 24, 2011, a user using the IP address 212.117.160.123 logged into Mt. Gox Account 2, Mt. Gox Account 3, and Liberty Reserve Account 1, as well as another Liberty Reserve account registered to Sterlingov (Liberty Reserve Account 2).

Sterlingov had also registered a third Liberty Reserve account (Liberty Reserve Account 3) using a different email address: [email protected]. Liberty Reserve records revealed that Liberty Reserve Account 2 was registered in Sterlingov’s name using the email address [email protected] which was the same email address linked to Mt. Gox Account 1. Information from the third Liberty Reserve account included a residential address in Gothenburg, Sweden which corresponded to Sterlingov’s home address. Both the second and third Liberty Reserve accounts were registered with the same Swedish telephone number which was registered to Sterlingov.
On August 25, 2012, Sterlingov’s Mt. Gox account received a 180 Bitcoin deposit from an account at the Bitcoin exchange BTC-e. Investigators examined the BTC-e account associated with the transaction. They learned the account belonged to Sterlingov with the email address [email protected].
Previously: DOJ Files $100 Million Civil Complaint Against BTC-e
Investigators obtained a search warrant for the Google account associated with the above Gmail address. A Google Drive folder belonging to the account contained a Russian language document titled Ввод денег (“Putting Money”). The document contained notes on layering funds that matched the “steps that Sterlingov took to pay for the domain www.bitcoinfog.com.”
An arrest warrant was issued for Sterlingov and U.S. law enforcement arrested him on April 27, 2021, at the Los Angeles International Airport. Sterlingov faces charges for money laundering, operating an unlicensed money transmitting business, and money transmission without a license in the District of Columbia.
According to the United States Department of Justice, Roman Sterlingov, 32, has operated Bitcoin Fog since 2011. During its operation, Bitcoin Fog moved 1.2 million Bitcoin worth $335 million at the time of the transactions.
The bulk of this cryptocurrency came from darknet marketplaces and was tied to illegal narcotics, computer fraud and abuse activities, and identity theft.

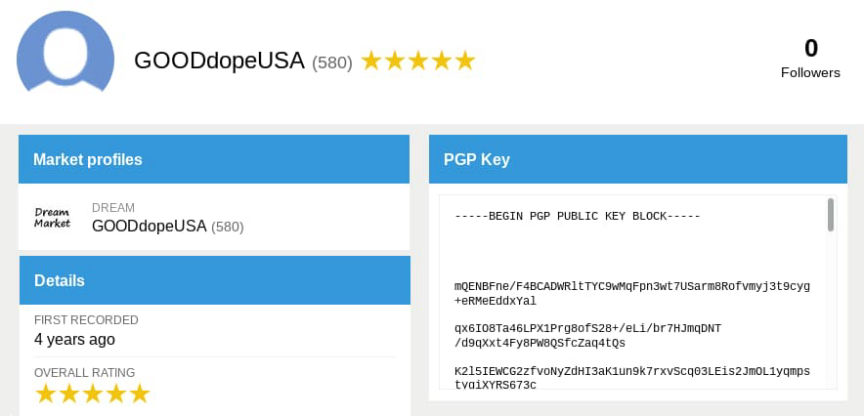
A screenshot of Bitcoin Fog in action | CoinTelegraph
IRS-CI cyber analysts identified direct deposits into Bitcoin Fog from at least 35 darkweb markets. Below are the top five markets by U.S. dollar value of deposits:
Undercover feds messaged Bitcoin Fog with details about their own criminal transactions.
IRS-CI cyber analysts identified funds sent directly from Bitcoin Fog to at least 51 different darknet markets. Below are the top five markets by the dollar value of sends:
An analysis of bitcoin transactions, financial records, internet service provider records, e-mail records, and additional investigative information, identifies Roman Sterlingov as the operator of Bitcoin Fog, according to a Criminal Complaint filed in the District Of Columbia District Court.
Early in the investigation, investigators with the Internal Revenue Service-Criminal Investigation (IRS-CI) associated Bitcoin Fog with the Hotmail address [email protected]. An account on the BitcoinTalk.org forum had announced the launch of Bitcoin Fog (Here is the archived announcement on BitcoinTalk.org). The person responsible for creating that account had signed up with the above Hotmail address and the name “Akemashite Omedetou.” Records from Microsoft pertaining to [email protected] revealed that the account was created on October 7, 2011, using an apparent fake name via a virtual private network. The account on BitcoinTalk.org included details about the Bitcoin Fog service, including the service’s clearnet URL, bitcoinfog.com.
Bitcoinfog.com was registered through Highhosting.net on October 25, 2011. WhoIs records showed that the domain was registered to “Akemashite Omedetou” with the email address [email protected]. Records from Highhosting.net revealed that Akemashite Omedetou used a Liberty Reserve account to pay for the domain. Liberty Reserve records showed that the account was registered to [email protected]. Investigators reviewed account activity associated with the Liberty Reserve account and linked Sterlingov to “a series of layered transactions through multiple payment platforms.”
Specifically:
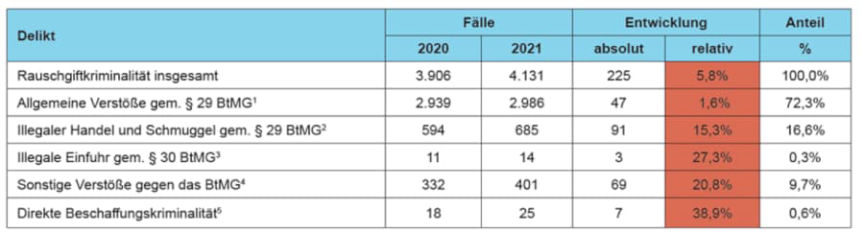
A chart of the laying steps allegedly taken by Sterlingov
Investigators analyzed the IP addresses used to access the above Liberty Reserve and Mt. Gox accounts. The analysis revealed Sterlingov as the common owner, according to an IRS-CI Special Agent Devon Beckett. For example, on November 24, 2011, a user using the IP address 212.117.160.123 logged into Mt. Gox Account 2, Mt. Gox Account 3, and Liberty Reserve Account 1, as well as another Liberty Reserve account registered to Sterlingov (Liberty Reserve Account 2).

Yes, it appears so.
Sterlingov had also registered a third Liberty Reserve account (Liberty Reserve Account 3) using a different email address: [email protected]. Liberty Reserve records revealed that Liberty Reserve Account 2 was registered in Sterlingov’s name using the email address [email protected] which was the same email address linked to Mt. Gox Account 1. Information from the third Liberty Reserve account included a residential address in Gothenburg, Sweden which corresponded to Sterlingov’s home address. Both the second and third Liberty Reserve accounts were registered with the same Swedish telephone number which was registered to Sterlingov.
On August 25, 2012, Sterlingov’s Mt. Gox account received a 180 Bitcoin deposit from an account at the Bitcoin exchange BTC-e. Investigators examined the BTC-e account associated with the transaction. They learned the account belonged to Sterlingov with the email address [email protected].
Previously: DOJ Files $100 Million Civil Complaint Against BTC-e
Investigators obtained a search warrant for the Google account associated with the above Gmail address. A Google Drive folder belonging to the account contained a Russian language document titled Ввод денег (“Putting Money”). The document contained notes on layering funds that matched the “steps that Sterlingov took to pay for the domain www.bitcoinfog.com.”
An arrest warrant was issued for Sterlingov and U.S. law enforcement arrested him on April 27, 2021, at the Los Angeles International Airport. Sterlingov faces charges for money laundering, operating an unlicensed money transmitting business, and money transmission without a license in the District of Columbia.

