A Warning About Darkweb Market Phishing Sites
As marketplaces struggle to provide current and working mirror links, bad actors have been creating and launching hundreds of sites aimed at phishing the credentials of darkweb market users and emptying the wallets of their market accounts. Phishing links are at an all time high for marketplaces but also for sites where users find their links, such as Dark.fail or Darknetlive.
Although this phishing is nothing new, a surprisingly high number of darkweb market users still lose money to by accessing a darkweb market through a site designed to steal their credentials. We have several easily identifiable types of phishing sites in existence right now.
Overview
Since most users get their market, forum, or other onion links through clearnet sites such as Dark.fail or Darknetlive, the entities behind these phishing operations have targeted both this site and Dark.fail through dozens of different methods of attack.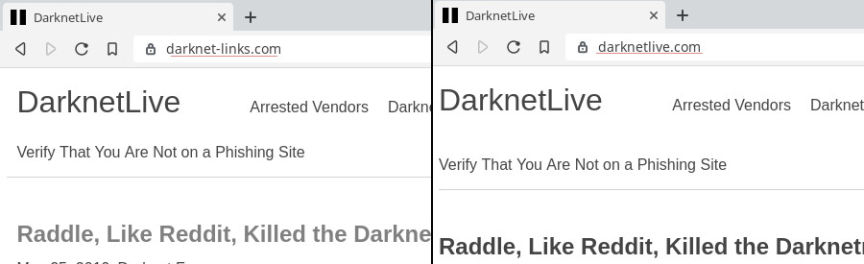
Right now we have a mix of mirrored websites and impersonation. When DeepDotWeb still functioned, the majority of the phishing attacks targetting DeepDotWeb users utilized typosquatting, counting on the user to make a typographical error when entering DeepDotWeb.com into the address bar. We had DeepDogWeb.com, DeeepDotWeb.com, and dozens of similar variations. Although those problems still exist, marketplaces are dealing with other issues. Although some actors have launched copies of Darknetlive and dark.fail with similar URLs, the majority of the attacks take different form.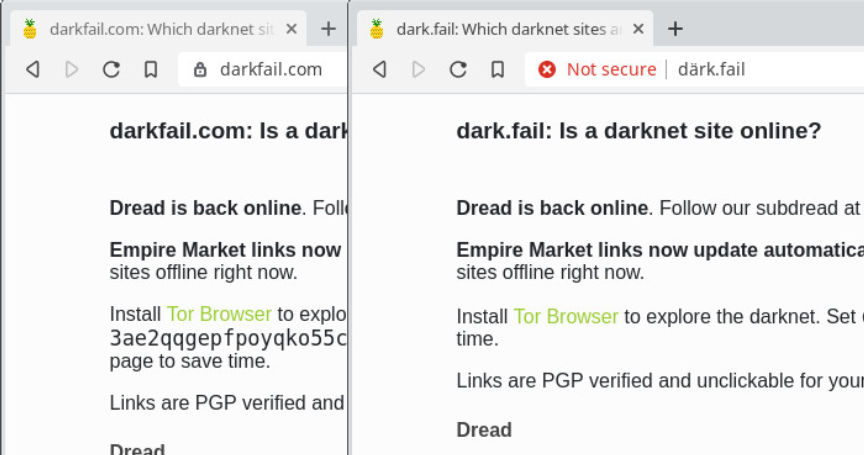
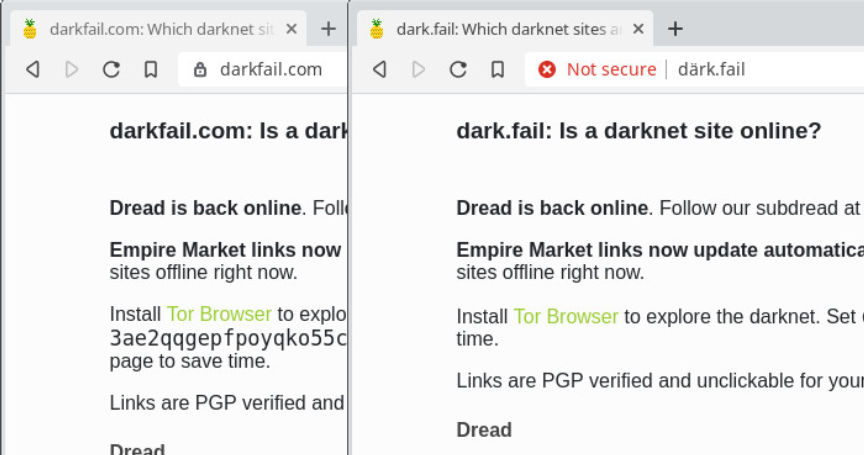
An example of a Dark.fail clone with a different TLD and a one with a homoglyph address.
Helpful-URL.com
Disregarding phishing links shared directly to unsuspecting users through Reddit or Dread private messages, one of the most prolific and successful attacks masquerades as a site affiliated with the phished marketplace. These sites are optimized for modern search engines and the URLs alone help them rank higher than sites offering legitimate links. These are not malicious versions of the hidden wiki; instead, each instance is created to phish users of a specific marketplace.
We will use Empire Market as an example. Nobody knows the Empire Market onion address without looking it up. Very few people have memorized more than a handful of onion addresses. And the links are even more difficult to remember now that they change hourly. The ongoing denial of service attacks against hidden services has rendered link verification through PGP verification almost impossible. So checking links found through a quick search for them might not be an option.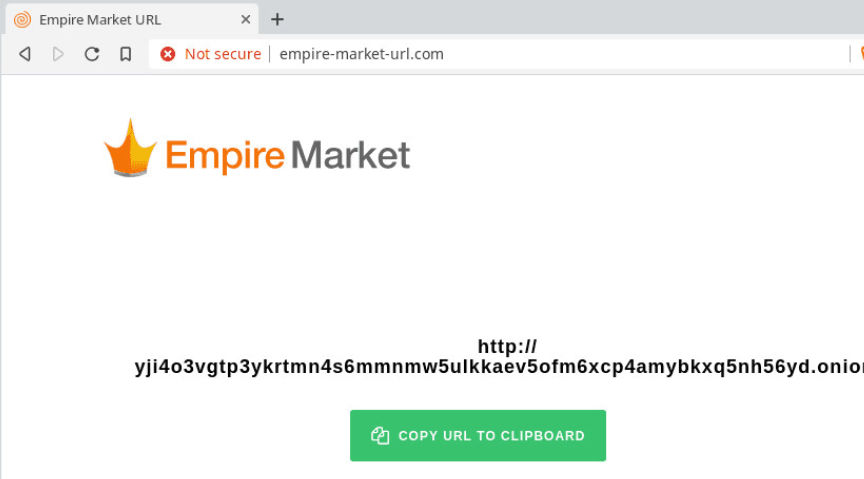
One of this actor’s phishing sites for Empire Market is empire-market-url.com. The site is ranked fairly high in Google search results. Not as high as some of the scammer’s other sites (top five), but high nonetheless. Someone frantically checking every site for working mirrors would easily find the site in question and visit one of the many mirrors listed on the site. The site currently has links that legitimately load Empire Market, even when the majority of the market’s links get killed.
Markets during periods of heavy load are often impossible to use through the links publicly provided by the market. Private mirrors, such as those for vendors, usually continue to work as to allow vendors to more reliable access the site. Vendors, for the most part, have an unspoken agreement not to share the vendor mirrors.
As for the empire-market-url proxy – I do not know how it works while Empire’s public mirrors are down. As far as I can tell, it is not mirroring a vendor mirror as the vendor mirrors have a visible element identifying them as private addresses for vendors. Se7en, an Empire Market staff member, confirmed on Dread that the phishing sites likely had access to private mirrors.
Once a user accesses Empire Market through one of the phishing proxies, all the .onion mirrors on the homepage are rewritten in order to keep the user within the phisher’s network. Aside from speed differences, no real differences would stand out to a user already vulnerable to this type of attack. The user can shop as usual. The user will then visit the market’s wallet. This is where the proxied version of the market really differs from the original version. Instead of generating a new address for the user, phishing variant of the market rewrites the bitcoin address shown to the user. When this happens, there is a noticeable lag where the phishing site is “generating addresses.” It is most likely making an RPC call to a bitcoin node but I have not investigated this further.
The real market generates an address for the user. The generated address comes with a signed message that verifies the date, the key, and the username of the user responsible for the key generation. All addresses begin with the digit “3” and have not been used by anyone.
Oddly enough, sometimes the phishing sites do not rewrite the bitcoin addresses. I have not determined why it seems to happen at random.
Even More Phishing
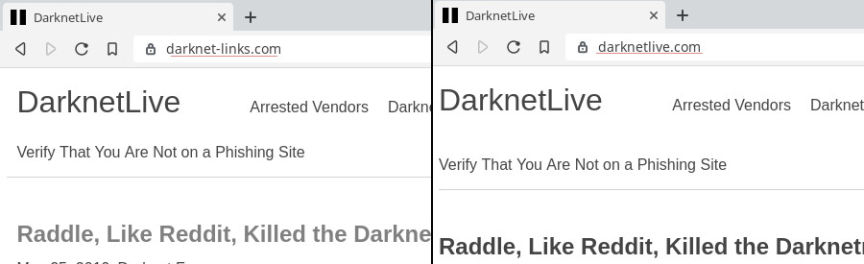
The same sites that list these fake marketplace addresses also redirect users to fake versions of Darknetlive and Dark.fail. In the Empire-market-url example, the footer of the page has a link to nightmare-market-urls.com, darkwebnews.info, darkwebdrugs.online, and darknet-links.com. The first link, nightmare-market-urls, is basically the Nightmare version of the Empire phishing site mentioned in the paragraph above. The other three links all serve a proxified version of Darknetlive.com.
The fake Darknetlive sites also serve fake links. For instance, Darknetlive has a link to Dark.fail. The fake verisons of this site change every instance of “dark.fail” to read “darkfail.com.” Of course, capitalizing Dark.fail bypasses this. Notice in the screenshot below how the onion address for Dark.fail has been changed but not the capitlized clearnet URL.
The real Dark.fail hidden service address is darkfailllnkf4vf.onion.
The capital letter thing is also shared by crimewave’s phishing legacy, Rotten Onions.
Lists of Fake Sites
The following list of phishing sites are hosted on 87.120.254.45.agarta-market-url.comagartha-market-url.comcannazon-market-url.comcore-market-url.comcoremarket-url.comcryptonia-market-url.comdarkfail.comdarknet-links.comdarkweb-links.comdarkweb-markets.comdarkweb-urls.comdarkwebdrugs.onlinedarkwebnews.infodream-market-urls.comdreammarket-drugs.infodreammarket-howto.infodreammarket-links.infodreammarket-url.comdreammarkettor.infoempire-market-url.comempiremarket-urls.comempiremarket.linkgenesis-market-url.comnightmare-market-url.netnightmare-market-urls.comnightmare-url.marketnightmaremarket-url.comwallst-market-url.comwallstreet-market-url.comwww.agarta-market-url.comwww.agartha-market-url.comwww.berlusconi-market-url.comwww.cannazon-market-url.comwww.core-market-url.comwww.coremarket-url.comwww.cryptonia-market-url.comwww.darkfail.comwww.darknet-links.comwww.darkweb-links.comwww.darkweb-markets.comwww.darkweb-urls.comwww.darkwebdrugs.onlinewww.darkwebnews.infowww.dream-market-urls.comwww.dreammarket-drugs.infowww.dreammarket-howto.infowww.dreammarket-links.infowww.dreammarket-url.comwww.dreammarkettor.infowww.empire-market-url.comwww.empiremarket-urls.comwww.empiremarket.linkwww.genesis-market-url.comwww.nightmare-market-url.netwww.nightmare-market-urls.comwww.nightmare-url.marketwww.nightmaremarket-url.comwww.wallst-market-url.comwww.wallstreet-market-url.com
The majority of the above links link to either Darknetlive or Dark.fail if they do not contain the name of a marketplace in the URL.
There’s also the great homoglyph därk.fail (aka xn–drk-qla.fail) and the vowel-swap dork.fail. Neither seem to be a part of the *-URL.com phishing campaign.
Even though his marketplace phishing links are doing fairly well in search engines, his phishing clones of darknetlive are dropping in rank. Some more quickly than others. And some of them hardly received any traffic to begin with…

Although this phishing is nothing new, a surprisingly high number of darkweb market users still lose money to by accessing a darkweb market through a site designed to steal their credentials. We have several easily identifiable types of phishing sites in existence right now.
Overview
Since most users get their market, forum, or other onion links through clearnet sites such as Dark.fail or Darknetlive, the entities behind these phishing operations have targeted both this site and Dark.fail through dozens of different methods of attack.
Empire Market URL “More LInks”
Right now we have a mix of mirrored websites and impersonation. When DeepDotWeb still functioned, the majority of the phishing attacks targetting DeepDotWeb users utilized typosquatting, counting on the user to make a typographical error when entering DeepDotWeb.com into the address bar. We had DeepDogWeb.com, DeeepDotWeb.com, and dozens of similar variations. Although those problems still exist, marketplaces are dealing with other issues. Although some actors have launched copies of Darknetlive and dark.fail with similar URLs, the majority of the attacks take different form.
Empire Market URL “More LInks”
An example of a Dark.fail clone with a different TLD and a one with a homoglyph address.
Helpful-URL.com
Disregarding phishing links shared directly to unsuspecting users through Reddit or Dread private messages, one of the most prolific and successful attacks masquerades as a site affiliated with the phished marketplace. These sites are optimized for modern search engines and the URLs alone help them rank higher than sites offering legitimate links. These are not malicious versions of the hidden wiki; instead, each instance is created to phish users of a specific marketplace.
We will use Empire Market as an example. Nobody knows the Empire Market onion address without looking it up. Very few people have memorized more than a handful of onion addresses. And the links are even more difficult to remember now that they change hourly. The ongoing denial of service attacks against hidden services has rendered link verification through PGP verification almost impossible. So checking links found through a quick search for them might not be an option.
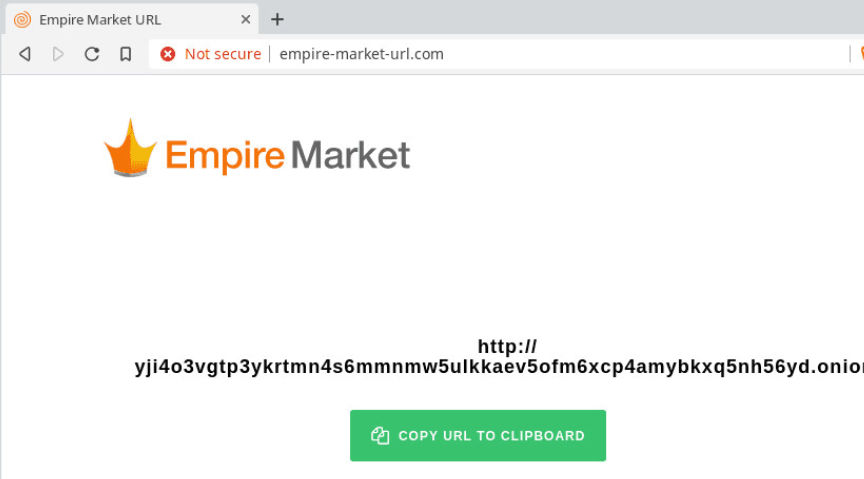
Empire Market URL “More LInks”
One of this actor’s phishing sites for Empire Market is empire-market-url.com. The site is ranked fairly high in Google search results. Not as high as some of the scammer’s other sites (top five), but high nonetheless. Someone frantically checking every site for working mirrors would easily find the site in question and visit one of the many mirrors listed on the site. The site currently has links that legitimately load Empire Market, even when the majority of the market’s links get killed.
Markets during periods of heavy load are often impossible to use through the links publicly provided by the market. Private mirrors, such as those for vendors, usually continue to work as to allow vendors to more reliable access the site. Vendors, for the most part, have an unspoken agreement not to share the vendor mirrors.
As for the empire-market-url proxy – I do not know how it works while Empire’s public mirrors are down. As far as I can tell, it is not mirroring a vendor mirror as the vendor mirrors have a visible element identifying them as private addresses for vendors. Se7en, an Empire Market staff member, confirmed on Dread that the phishing sites likely had access to private mirrors.
Once a user accesses Empire Market through one of the phishing proxies, all the .onion mirrors on the homepage are rewritten in order to keep the user within the phisher’s network. Aside from speed differences, no real differences would stand out to a user already vulnerable to this type of attack. The user can shop as usual. The user will then visit the market’s wallet. This is where the proxied version of the market really differs from the original version. Instead of generating a new address for the user, phishing variant of the market rewrites the bitcoin address shown to the user. When this happens, there is a noticeable lag where the phishing site is “generating addresses.” It is most likely making an RPC call to a bitcoin node but I have not investigated this further.
The real market generates an address for the user. The generated address comes with a signed message that verifies the date, the key, and the username of the user responsible for the key generation. All addresses begin with the digit “3” and have not been used by anyone.
Oddly enough, sometimes the phishing sites do not rewrite the bitcoin addresses. I have not determined why it seems to happen at random.
Even More Phishing
The same sites that list these fake marketplace addresses also redirect users to fake versions of Darknetlive and Dark.fail. In the Empire-market-url example, the footer of the page has a link to nightmare-market-urls.com, darkwebnews.info, darkwebdrugs.online, and darknet-links.com. The first link, nightmare-market-urls, is basically the Nightmare version of the Empire phishing site mentioned in the paragraph above. The other three links all serve a proxified version of Darknetlive.com.
The fake Darknetlive sites also serve fake links. For instance, Darknetlive has a link to Dark.fail. The fake verisons of this site change every instance of “dark.fail” to read “darkfail.com.” Of course, capitalizing Dark.fail bypasses this. Notice in the screenshot below how the onion address for Dark.fail has been changed but not the capitlized clearnet URL.
The real Dark.fail hidden service address is darkfailllnkf4vf.onion.
The capital letter thing is also shared by crimewave’s phishing legacy, Rotten Onions.
Lists of Fake Sites
The following list of phishing sites are hosted on 87.120.254.45.agarta-market-url.comagartha-market-url.comcannazon-market-url.comcore-market-url.comcoremarket-url.comcryptonia-market-url.comdarkfail.comdarknet-links.comdarkweb-links.comdarkweb-markets.comdarkweb-urls.comdarkwebdrugs.onlinedarkwebnews.infodream-market-urls.comdreammarket-drugs.infodreammarket-howto.infodreammarket-links.infodreammarket-url.comdreammarkettor.infoempire-market-url.comempiremarket-urls.comempiremarket.linkgenesis-market-url.comnightmare-market-url.netnightmare-market-urls.comnightmare-url.marketnightmaremarket-url.comwallst-market-url.comwallstreet-market-url.comwww.agarta-market-url.comwww.agartha-market-url.comwww.berlusconi-market-url.comwww.cannazon-market-url.comwww.core-market-url.comwww.coremarket-url.comwww.cryptonia-market-url.comwww.darkfail.comwww.darknet-links.comwww.darkweb-links.comwww.darkweb-markets.comwww.darkweb-urls.comwww.darkwebdrugs.onlinewww.darkwebnews.infowww.dream-market-urls.comwww.dreammarket-drugs.infowww.dreammarket-howto.infowww.dreammarket-links.infowww.dreammarket-url.comwww.dreammarkettor.infowww.empire-market-url.comwww.empiremarket-urls.comwww.empiremarket.linkwww.genesis-market-url.comwww.nightmare-market-url.netwww.nightmare-market-urls.comwww.nightmare-url.marketwww.nightmaremarket-url.comwww.wallst-market-url.comwww.wallstreet-market-url.com
The majority of the above links link to either Darknetlive or Dark.fail if they do not contain the name of a marketplace in the URL.
There’s also the great homoglyph därk.fail (aka xn–drk-qla.fail) and the vowel-swap dork.fail. Neither seem to be a part of the *-URL.com phishing campaign.
Even though his marketplace phishing links are doing fairly well in search engines, his phishing clones of darknetlive are dropping in rank. Some more quickly than others. And some of them hardly received any traffic to begin with…

Lol Weak Ass Proxy

